Creating Trust Online

Comodo Anti-Spam Gateway is an advanced email filtering solution designed to free employee's inboxes of Junk Mail Glut. It is cloud-based, which is ideally suited for small to mid-size businesses.

Malware authors, spammers & 'phishers' have joined forces in an effort to socially engineer end-users to open email attachment or click on phishing links redirecting to malicious websites, thus infecting the host with viruses, Rrojans, spyware, rootkits & backdoors leading to the theft of confidential data and causing the infected system to be absorbed into global botnets.

Most mail-client software (e.g Microsoft Outlook) has a preview function that displays e-mail content. Pornographic, offensive, religiously or socially objectionabe material will be automatically exhibited which may lead to legal action against the employers failure to apply due diligence in not procuring readily available counter-measures to shield objectionable material.

Most spam email contains hidden tracking allowing the sender to identify which email addresses reviewed its messages - even in preview mode. This causes spam volumes to increase exponentially, but it may also cause a failure in regulatory compliance. For example, the data protection Act (U.K.), which dicatates that it is the company's responsibility to control any data sent from its email addresses.

For companies that have their own mail servers, or hosted mailboxes, spam consumes storage. Mail data stores or pay-per-Gigabyte cloud solutions often rapidly fill with junk mail requiring that more storage be purchased.

Up to 80% of incoming traffic is spam. This interrupts regular network traffic, slowing down legitimate inbound communication also known as bandwidth starvation.

ISPs have to pay for the bandwidth that they resell to their customers, the more they have to buy to offset the volumes of customer spam consuming their bandwidth the more they have to charge the end-user

Spammers increasingly use 'hijacked'mail servers to send their spam. This helps them remain anonymous in their inability to send or receive legitimate email.

Mail servers administrators have to devote otherwise productive time to clean spam messages out of mailboxes in order to keep the server's mail stores operating at optimum capacity.

For every ten spam messages received per hour, at a rate of 3 seconds for identification and deletion, nearly 3 hours per month or 4 fully paid days per year are spent on inbox house keeping

Email from banks, clearing houses, online retailers and social networking sites have to be carefully scrutinized to ensure that they are genuine and not being used to mislead recipients to disclose sensitive information with the intension of conducting fraudulent transactions on behalf of the organisation or its users.
Total elimination of email-borne malware threats to your network and data Elimination of wasted bandwidth due to unwanted email traffic Granular, centralized control of user- and group-based email policies Audit, litigation, and forensic support with comprehensive logging Fast, simple deployment with Active Directory/LDAP integration
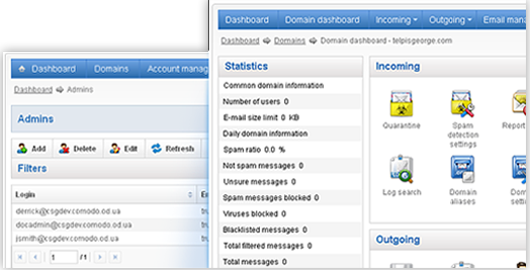
It has a centralized, web based management console which makes it simple for administrators to set up, add users and domains, configure mail blacklists and whitelists and manage quarantined emails.
Only comodo combines the total security of a default-deny environment with the flexibility and operational freedom to default-allow. This game changing innovation solves the email security problem
Gateway-level filtering without the dedicated hardware deals with spam before it enters the corporate network.
Comodo uses innovative technologies integrated into the Comodo Antispam Gateway:
Valkyrie - a cloud-based system that uses multiple analytic techniques, as well as in-depth human expertise, to score incoming email attachments as good, bad, or unknown. Unknown files are placed in containment for further analysis, and allowed to pass on to the user.

Please Contact Us
enterprisesales.india@comodo.com